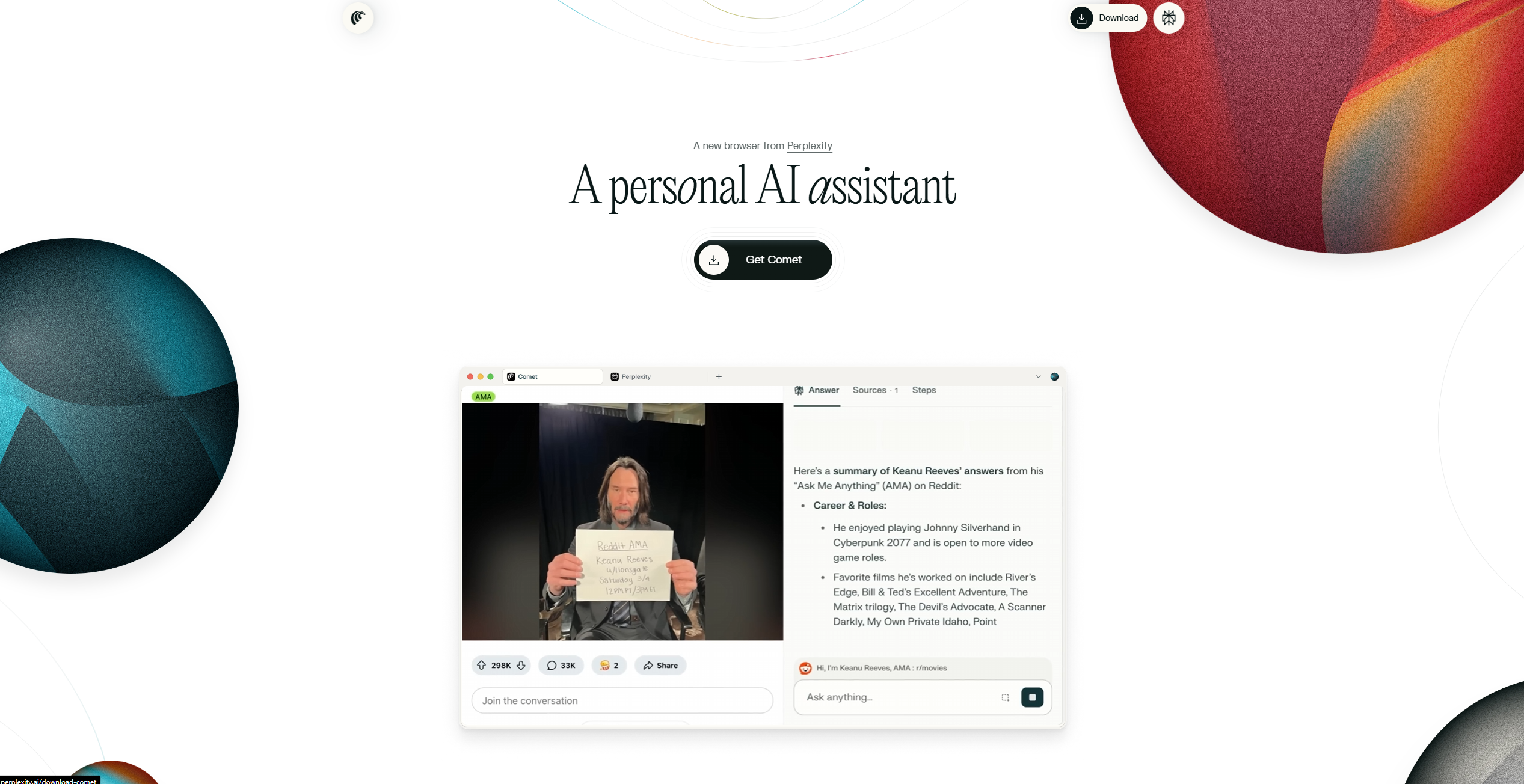
About Comet
Advertiser Disclosure: Futurepedia.io is committed to rigorous editorial standards to provide our users with accurate and helpful content. To keep our site free, we may receive compensation when you click some links on our site.
Key Features
- Agentic Task Automation: Automates multi-step actions, including product research and purchase, meeting scheduling, and inbox management.
- Cross-Tab Context Awareness: Maintains memory across tabs and browsing sessions, allowing users to continue tasks without re-entering information.
- Integrated Productivity Tools: Connects with Gmail, Google Calendar, and Google Drive, enabling users to complete communication and scheduling tasks within the browser.
- Chromium Compatibility: Built on Chromium, supporting Chrome extensions, bookmark imports, and enterprise policies for easy adoption.
- Enterprise-Grade Security: Provides compliance with SOC 2, HIPAA, and GDPR standards, ensuring that sensitive information is managed securely.
Pros & Cons
Pros
- Time Efficiency: Reduces the need for manual task handling, saving hours on repetitive workflows.
- Contextual Continuity: Preserves context across browsing activities, minimizing disruption and tab overload.
- Proactive Intelligence: Offers reminders and suggestions that help keep tasks on track.
- Enterprise Ready: Meets strong compliance requirements, making it suitable for businesses with high data security needs.
- User Familiarity: Retains the layout and structure of traditional Chromium browsers, lowering the learning curve.
Cons
- High Pricing Barrier: Currently available only to Perplexity Max subscribers at $200 per month, limiting accessibility.
- Early-Stage Development: Some features remain experimental and may not yet deliver consistently polished results.
- Agentic Security Concerns: AI task automation can occasionally be vulnerable if misdirected, creating risks in sensitive workflows.